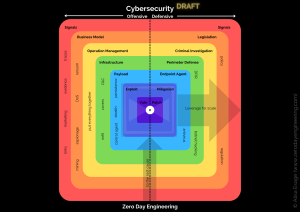
This course covers key aspects of cybersecurity, including understanding threats, vulnerabilities, and the necessary countermeasures. It may also delve into specialized areas such as zero-day vulnerability research.
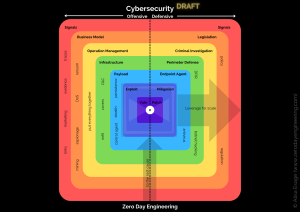
This course covers key aspects of cybersecurity, including understanding threats, vulnerabilities, and the necessary countermeasures. It may also delve into specialized areas such as zero-day vulnerability research.
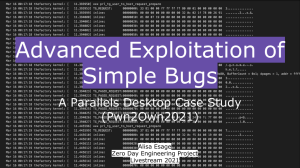
At Pwn2Own Vancouver 2021 I have demonstrated an 0day VM escape exploit for Parallels Desktop hypervisor. The exploit chain that I developed was based on logic issues. In this deep technical presentation I will share the technical details of the exploit, as well as various preliminary and contextual knowledge related to it.
Logic security vulnerabilities (i.e. those that can be exploited without any memory corruptions) are becoming increasingly important in offensive security research right now, as Rust and other memory-safe programming languages are rapidly taking over popular code bases. When evaluating the attack surface of Parallels Desktop, as an expert in both hypervisors and memory corruption bugs, I saw many opportunities for classical buffer overflows, but chose to try and find a logic bug instead. As hypervisors are ultra-complex low level software, exploitable logic bugs in them are extremely rare. I was lucky to find such a “one of a kind” bug.
Despite the bug was quite simple, the exploit turned out to be not so easy. Exploitation of the bug required me to develop a kernel module for the guest OS from which I was escaping, reverse-engineer some internal RPC protocol of the hypervisor, and emulate it in the exploit code. Eventually the exploit was reliable 100% by design, and executed arbitrary code on the host Mac. During the Pwn2Own competitions it came as a surprize that my exploit did not meet any collisions with other competition entries. Because the bug itself was quite easy, I expected that at least one participant would find and utilize it independently in their own Pwn2Own exploit. But it didn’t happen. That made me aware of the fact that a bug that looks easy does not necessarily imply an easy discovery or an easy exploitation process, an estimation which is very important for strategic aspects of offensive security research.

We will look into how we can bypass kASLR, kLFH, and do hands-on exploitation using data-only attack, which effectively bypasses SMEP and other exploit mitigations.
Upon completion of this training, participants will be able to learn:

Burp Suite Pro is the leading tool for auditing Web applications at large, but also a complex beast where new features get added every few weeks. Mastering Burp Suite Pro, including its newest features, allows testers to get the most out of the tool, optimizing time spent auditing and testing. Work will be faster (hotkeys!) and much more efficient (more tools, more possibilities!). Attendees will also learn to measure and assess the quality of their attacks, a crucial skill in real-life engagements that can make the difference between a false-negative and a critical finding.

Full Stack Web Attack is not an entry-level course. It’s designed to push you beyond what you thought was possible and set you on the path to develop your own workflow for offensive zero-day web research.
This course is developed for web penetration testers, bug hunters and developers that want to make a switch to server-side web security research or see how serious adversaries will attack their web based code.
Students are expected to know how to use Burp Suite and have a basic understanding of common web attacks as well as perform basic scripting using common languages such as python, PHP and JavaScript. Each of the vulnerabilities presented have either been mirrored from real zero-day or are n-day bugs that have been discovered by the author with a focus on not just exploitation, but also on the discovery.
So if you want to learn how to exploit web technologies without client interaction for maximum impact, that is, remote code execution then this is the course for you.