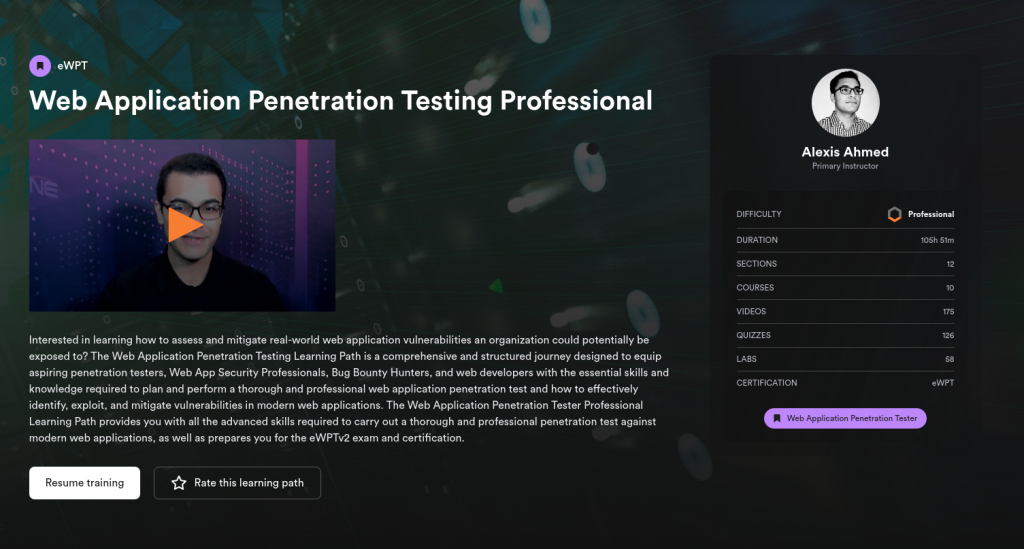
Interested in learning how to assess and mitigate real-world web application vulnerabilities an organization could potentially be exposed to? The Web Application Penetration Testing Learning Path is a comprehensive and structured journey designed to equip aspiring penetration testers, Web App Security Professionals, Bug Bounty Hunters, and web developers with the essential skills and knowledge required to plan and perform a thorough and professional web application penetration test and how to effectively identify, exploit, and mitigate vulnerabilities in modern web applications. The Web Application Penetration Tester Professional Learning Path provides you with all the advanced skills required to carry out a thorough and professional penetration test against modern web applications, as well as prepares you for the eWPTv2 exam and certification.