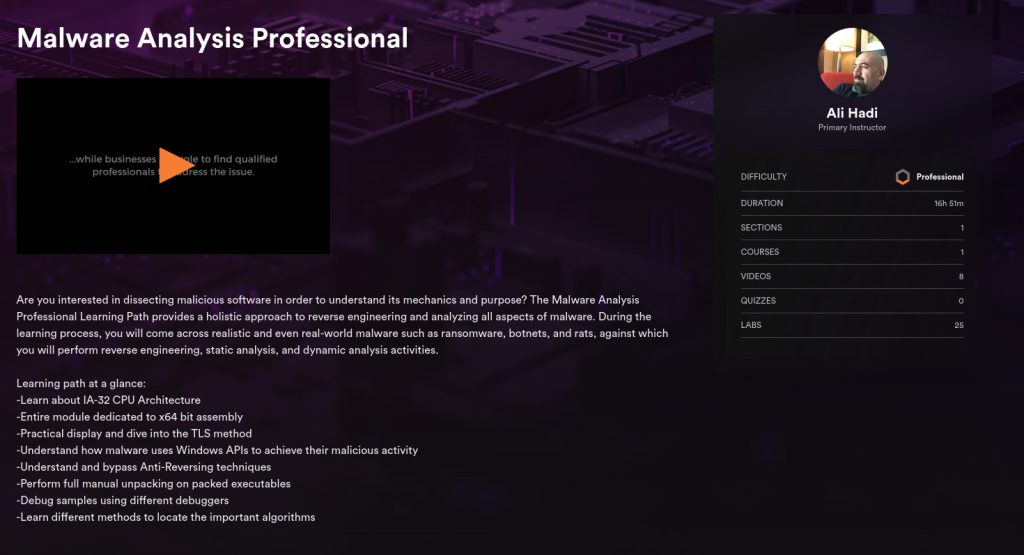
Are you interested in dissecting malicious software in order to understand its mechanics and purpose? The Malware Analysis Professional Learning Path provides a holistic approach to reverse engineering and analyzing all aspects of malware. During the learning process, you will come across realistic and even real-world malware such as ransomware, botnets, and rats, against which you will perform reverse engineering, static analysis, and dynamic analysis activities.
Learning path at a glance:
- Learn about IA-32 CPU Architecture
- Entire module dedicated to x64 bit assembly
- Practical display and dive into the TLS method
- Understand how malware uses Windows APIs to achieve their malicious activity
- Understand and bypass Anti-Reversing techniques
- Perform full manual unpacking on packed executables
- Debug samples using different debuggers
- Learn different methods to locate the important algorithms